There are 45 people at the workshop from nearly all faculties at Lancaster University, as well as participants from Manchester and London. The annual research program was introduced by Corinne May-Chahal (FASS) and Ruth Wodak (Chair, Academic Board, IAS).
Professor Cindy Weber introduced the key questions for the program: how is safe living conceived today? However conceived, is it livable? Adrian Mackenzie sketched the key facets of ‘safe living’ that later events in the annual research program will address. Mark Lacy discussed the desirability of a biometric iPod ready for the age of terror. The iPod would integrate security and entertainment. What composite possibilities would this allow?
More importantly, how would we begin to think about the possibilities of such a device? The workshop would start to do this by thinking about how political dynamics feed back into devices. A policy report from UK Cabinet Office, ‘Building on Progress: Security, Crime and Justice’ was chosen as one way to engage with the social, institutional, and design implications of the construction of such devices.
Roundtable on ‘Building on Progress: Security, Crime and Justice’
Professor Rachel Cooper (LICA, Imagination@Lancaster) spoke about a project done with the Home Office and the Design Council called ‘Design Against Crime.’ The project (2003) documented 30 case studies in which design had been used against crime. These were re-packaged by the Design Council as documents describing products that were inspiring, useful for training or learning in relation to various context: transport, education, shopping, etc. For instance, the DieHard battery (US) would no longer work as soon it was removed from a car. This protects against the widespread theft of batteries. Other examples include the re-design of the Dulux paint can to thwart a paint theft scam in Birmingham, or the re-development of social spaces to increase visibility, or fences built to prevent loitering in public spaces. A key goal was to develop materials that could be used for teaching in high school design classes in UK. A number of other initiatives were developed: design against crime competitions for students; professional development for designers. For instance, this was focused on design in retail, and involved police and retailers as well as designers.
Dr James Wilsdon (IAS/Demos) spoke about how security has come to the fore in political discourse, especially in the form of ‘liquid fear’ (Zygmunt Baumann). The key question is: what is being smuggled in under the rubric of security, safety and protection? This does not mean turning to conspiracy theory as Adam Curtis (see his documentaries: The Trap [concept of freedom and fear],
The Century of the Self [the roots of consumerism & PR] and The Power of Nightmares [comparing Neo conservatists with radical islamists] for instance, argues. How is security, safety and protection used to drive through policy decisions? From the perspective of science and innovation policy, there is a tendency to actually shut down debates even in the guise of opening up debate. The use of notion of risk is a good example since it often narrows debate down. The challenge of Chindia is also being used to drive policy decisions. We need to be suspicious and alert to these rhetorics of closure. Actually there is very little debate about these securities and fears. The Information Commissioner Richard Thomas is one exception to this. But Deborah Mathisons Citizen Juries of Mori’s polling data does not open up debate. There are sham consultations and debates, for instance, taking place on nuclear new build. The decision has already been taken. Calvino’s ‘Six Memos for the Next Millenium’ is a nice ethics to how things could be done differently.
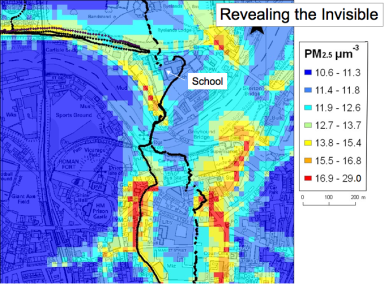
Dr Suzanne Regan (Department of Organisation, Work and Technology, Lancaster University) switched the focus to looking at some of the everyday practices that underlie protection. There were six papers published by Cabinet under the ‘Building on Progress’ theme. The ‘Families’ policy report looks, among things, at ‘disadvantaged’ families in the context of child protection services. For instance, the Basic Services Integrated Database will flag up children and families that social services may need to protect. The rise of child protection reports began with X-rays of battered babies at University of Colorado, Denver in the 1960s. This led to protocols and procedures for ‘child abuse.’ There has been a rise recently in the number of children identified as experiencing ’emotional abuse.’ This can be linked to police involvement in domestic violence disputes. Bureaucratic responses to complex problems in families need to be investigated. A case was discussed that illustrates the self-referential features that serve to exclude people. There are mismatches and disconnects between the procedures and discourses of protection and experience of people in this situation. ‘Information can disconfirm discursive identities’. A ‘simulacra of protection’ can result from these procedures and protocols. In every setting – police, criminal justice, social services – a similar simulacra can be found. How then to design safe living when such practices of exclusion are systematically enacted?
Dr Imogen Tyler (Sociology, Lancaster University) asked how ‘safe living’ and the desire to design out insecurity excludes and screens out certain groups? How does correctional design abject people? The figure of the asylum seeker was once termed a refugee. Such people come seeking safety or a haven, but increasingly don’t get what they come for. This figure has been fetishised in many ways. The imaginative geography of detention is a key site for policy, design and debate. Immigration and detention industries are pivotal. What challenges to abjected populations are possible? The protection of a safe group always engenders the unsafe, the unprotected. The government is explicitly committed to private detention facilities in the ‘Building on Progress’ reports. The UK government is also re-considering its commitment to human rights legal instruments. This too is mentioned in the report.
Reporting centres for asylum seekers are one place to begin thinking about this concretely. The reporting centre in Glasgow is a hard place to imagine in some ways. It places the myth of national hospitality in question. The UK government has the widest governmental powers to detain and remove in the EU. Now the very act of seeking asylum has become the ground for detention in many states. The fortification of boundaries introduces ‘states within a state.’ There is a booming commerce in asylum, safe living and protection. Who profits? In addition to regular prisons, there are 13 detention centres. 7 of them are run under contract. We can’t actually just look at government policy because of the way in which corporate interests are driving events. They want to keep facilities expanding and full, even as asylum applications fall. For instance, Global Solutions Limited runs prisons and detention centres. It has a totally monopoly on Australia’s detention centres. It’s slogan is ‘people are our business; our business is our people.’ The facts and figures on these centres are difficult to find. They are closed and visited by few people. No cameras or phones are allowed, apart from payphones. This is an unmapped industry. There is a feedback mechanism that runs through mass media that ratchets up developments in this area. The detention centre is hyper-visible in the news media. They are imagined as spaces of anger or luxury, even though little is known about them. Deliberate conflation of different categories of people occurs. Asylum seeking has become criminalised in UK, interchangeably with the figure of the terrorist. What is missing here? The actual people. What happens to the surplus population? What does it mean that government is going to review its human rights obligations? What about ethics? What about unsafe live, communities of resistance, means of interfering or designing unsafe spaces?
Professor Michael Dillon (Politics and International Relations, Lancaster University) looked to some of the wider conceptual issues to begin with. In a sense, we have discussed an architecture of security as an imaginary. It is a dominant imaginary. The logo of the ARP is an open safety pin, an everyday object. It can be a weapon, especially when it is open. There is constant slippage between weapon and openness. It has an ambivalence. Cicero was famous for this motto: the safety [salus] of the people is the supreme law. All security discourse constitute political communities. They are integral to who and what we think we are. There is no discourse on security without fear and terror. Design and security have an ancient connection. For instance, crusader castles reflect this. But we are in a boom time for security design. There is a shift from prophylactic security design to something complementary, the design of safe living. When life is the referent object, what difference does that make? All referent objects give rise to different epistemologies and politics. Securing life raises different problems to securing the nation-state. The latter concern leads to prophylactic security design. If you take life as referent object, then different design problem arise.
There are different conceptions of life that might become object of concern. Life here is a biological function. This informs the dominant security imaginary today. Sometimes this is confined to human life as biological life. But other forms of life are recognised, especially animal life. Across these, complexity arises from closely connected interactions that lead to non-linear transformations, change, unpredictability and contingency. Life-like systems evolve. Life displays further contingency and aleatory features.
In a policy forum, risk is one way to describe these. Risk is the commodification of change and exposure to contingency. Life circulates, and living systems are futural. Life is ‘evental’ in many senses that elicit calculation, management strategies, and contingency planning. Transformations in life include demographic, digitalisation, and molecularisation facets. For instance, chronic illness is always already at work in our lives, and this elicits demographical, digitalising and molecularising processes that reach into the lives of population at critical junctures, or indeed, throughout life courses. The promotion of life, the production of life, relies on vital signs such as complexity, interactive adaptation, emergence, multi-genesis, and pluri-potency. The question is how to animate and engineer preferred forms of life. This ambition stretched from animal forms, human forms, to economic and social forms. The poetry of Donald Rumsfield offers a good way to summarise this ethos:
 The Unknown
The Unknown
As we know,
There are known knowns.
There are things we know we know.
We also know
There are known unknowns.
That is to say
We know there are some things
We do not know.
But there are also unknown unknowns,
The ones we don’t know
We don’t know.
—Feb. 12, 2002, Department of Defense news briefing
Filed under: workshop 1 | Tagged: asylum-seeker, children, closure, crime, life, politics | 1 Comment »